List of Windows Run Commands
Instead of navigating through a hundred Windows and dialogs, you can start a number of Windows’ utilities from the Start & Run ([Windows] + [R]) dialog itself.
Utility Run Command
Accessibility Controls . . . . . . . . . . . . .access.cpl
Accessibility Wizard . . . . . . . . . . . . . . . . . . . . . .accwiz
Add Hardware Wizard . . . . . . . . . . . . . ..hdwwiz.cpl
Add/Remove Programs . . . . . . . . . . . . . . . . . . .wiz.cpl
Administrative Tools . . . . . . . . . . . .control admintools
Adobe Acrobat (if installed) . . . . . . . . . . . . . . . .acrobat
Adobe Distiller (if installed) . . . . . . . . . . . . . . . .acrodist
Adobe Photoshop (if installed) . . . . . . . . . . . . .photoshop
Automatic Updates . . . . . . . . . . . . . . .. .wuaucpl.cpl
Bluetooth Transfer Wizard . . . . . . . . . . . . . . . . .fsquirt
Calculator . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .calc
Certificate Manager . . . . . . . . . . . . . .certmgr.msc
Character Map . . . . . . . . . . . . . . . . . . . . . . . . . .charmap
Check Disk Utility . . . . . . . . . . . . . . . . . . . . . . . .chkdsk
Clipboard Viewer . . . . . . . . . . . . . . . . . . . . . . . .clipbrd
Command Prompt . . . . . . . . . . . . . . . . . . . . . . .cmd
Component Services . . . . . . . . . . . . . . . . . . . . . .dcomcnfg
Computer Management . . . . . . . . . . . . . . . . . . .compmgmt.msc
Control Panel . . . . . . . . . . . . . . . . . . . . . . . . . . .control
Date and Time Properties . . . . . . . . . . . . . . . . .timedate.cpl
DDE Shares . . . . . . . . . . . . . . . . . . . . . . . . . . . . .ddeshare
Device Manager . . . . . . . . . . . . . . . . . . . . . . . . .devmgmt.msc
Direct X Control Panel (If Installed) . . . . . . . . .directx.cpl
Direct X Troubleshooter . . . . . . . . . . . . . . . . . . .dxdiag
Disk Cleanup Utility . . . . . . . . . . . . . . . . . . . . . .cleanmgr
Disk Defragment . . . . . . . . . . . . . . . . . . . . . . . . .dfrg.msc
Disk Management . . . . . . . . . . . . . . . . . . . . . . . .diskmgmt.msc
Disk Partition Manager . . . . . . . . . . . . . . . . . . .diskpart
Display Properties . . . . . . . . . . . . . . . . . . . . . . .control desktop OR desk.cpl
Display Properties (Appearance Tab) . . . . . . . .control color
Dr. Watson System Troubleshooting Utility . . .drwtsn32
Driver Verifier Utility . . . . . . . . . . . . . . . . . . . . .verifier
Event Viewer . . . . . . . . . . . . . . . . . . . . . . . . . . . .eventvwr.msc
Files and Settings Transfer Tool . . . . . . . . . . . .migwiz
File Signature Verification Tool . . . . . . . . . . . . .sigverif
Findfast . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .findfast.cpl
Firefox (if installed) . . . . . . . . . . . . . . . . . . . . . .firefox
Folders Properties . . . . . . . . . . . . . . . . . . . . . . .control folders
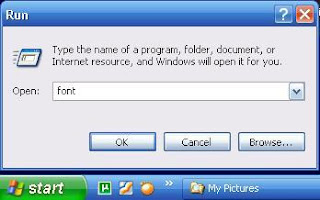
Fonts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .control fonts
Fonts Folder . . . . . . . . . . . . . . . . . . . . . . . . . . . .fonts
Free Cell Card Game . . . . . . . . . . . . . . . . . . . . . .freecell
Game Controllers . . . . . . . . . . . . . . . . . . . . . . . .joy.cpl
Group Policy Editor (XP Professional) . . . . . . .gpedit.msc
Hearts Card Game . . . . . . . . . . . . . . . . . . . . . . .mshearts
Help and Support . . . . . . . . . . . . . . . . . . . . . . . .helpctr
HyperTerminal . . . . . . . . . . . . . . . . . . . . . . . . . .hypertrm
Iexpress Wizard . . . . . . . . . . . . . . . . . . . . . . . . .iexpress
Indexing Service . . . . . . . . . . . . . . . . . . . . . . . . .ciadv.msc
Internet Connection Wizard . . . . . . . . . . . . . . . .icwconn1
Internet Explorer . . . . . . . . . . . . . . . . . . . . . . . .iexplore
Internet Properties . . . . . . . . . . . . . . . . . . . . . . .inetcpl.cpl
Internet Setup Wizard . . . . . . . . . . . . . . . . . . . .inetwiz
Java Control Panel (If Installed) . . . . . . . . . . . .jpicpl32.cpl
Java Control Panel (If Installed) . . . . . . . . . . . .javaws
Keyboard Properties . . . . . . . . . . . . . . . . . . . . .control keyboard
Local Security Settings . . . . . . . . . . . . . . . . . . . .secpol.msc
Local Users and Groups . . . . . . . . . . . . . . . . . . .lusrmgr.msc
Log Out Of Windows . . . . . . . . . . . . . . . . . . . . . .logoff
Malicious Software Removal Tool . . . . . . . . . . .mrt
Microsoft Access (if installed) . . . . . . . . . . . . . .access
Microsoft Chat . . . . . . . . . . . . . . . . . . . . . . . . . . .winchat
Microsoft Excel (if installed) . . . . . . . . . . . . . . .excel
Windows Movie Maker . . . . . . . . . . . . . . . . . . . .moviemk
Microsoft Paint . . . . . . . . . . . . . . . . . . . . . . . . . .mspaint OR pbrush
Microsoft Powerpoint (if installed) . . . . . . . . . .powerpnt
Microsoft Word (if installed) . . . . . . . . . . . . . . .winword
Microsoft Syncronization Tool . . . . . . . . . . . . . .mobsync
Minesweeper Game . . . . . . . . . . . . . . . . . . . . . .winmine
Mouse Properties . . . . . . . . . . . . . . . . . . . . . . . .control mouse
Mouse Properties . . . . . . . . . . . . . . . . . . . . . . . .main.cpl
Nero (if installed) . . . . . . . . . . . . . . . . . . . . . . . .nero
Netmeeting . . . . . . . . . . . . . . . . . . . . . . . . . . . . .conf
Network Connections . . . . . . . . . . . . . . . . . . . . . .control netconnections
Network Connections . . . . . . . . . . . . . . . . . . . . .ncpa.cpl
Network Setup Wizard . . . . . . . . . . . . . . . . . . . .netsetup.cpl
Notepad . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .notepad
Nview Desktop Manager (If Installed) . . . . . . .nvtuicpl.cpl
Object Packager . . . . . . . . . . . . . . . . . . . . . . . . .packager
On Screen Keyboard . . . . . . . . . . . . . . . . . . . . . .osk
Opens AC3 Filter (If Installed) . . . . . . . . . . . . . .ac3filter.cpl
Outlook Express . . . . . . . . . . . . . . . . . . . . . . . . .msimn
Password Properties . . . . . . . . . . . . . . . . . . . . .password.cpl
Performance Monitor . . . . . . . . . . . . . . . . . . . . .perfmon
Phone and Modem Options . . . . . . . . . . . . . . . .telephon.cpl
Phone Dialer . . . . . . . . . . . . . . . . . . . . . . . . . . . .dialer
Pinball Game . . . . . . . . . . . . . . . . . . . . . . . . . . . .pinball
Power Configuration . . . . . . . . . . . . . . . . . . . . .powercfg.cpl
Printers and Faxes . . . . . . . . . . . . . . . . . . . . . . .control printers
Printers Folder . . . . . . . . . . . . . . . . . . . . . . . . . .printers
Private Character Editor . . . . . . . . . . . . . . . . . .eudcedit (to create your own fonts)
Quicktime (If Installed) . . . . . . . . . . . . . . . . . . .QuickTime.cpl
Quicktime Player (if installed) . . . . . . . . . . . . . .quicktimeplayer
Real Player (if installed) . . . . . . . . . . . . . . . . . .realplay
Regional Settings . . . . . . . . . . . . . . . . . . . . . . . .intl.cpl
Registry Editor . . . . . . . . . . . . . . . . . . . . . . . . . .regedit
Remote Access Phonebook . . . . . . . . . . . . . . . .rasphone
Remote Desktop . . . . . . . . . . . . . . . . . . . . . . . . .mstsc
Removable Storage . . . . . . . . . . . . . . . . . . . . . .ntmsmgr.msc
Removable Storage Operator Requests . . . . . .ntmsoprq.msc
Resultant Set of Policy (XP Professional) . . . . .rsop.msc
Scanners and Cameras . . . . . . . . . . . . . . . . . . . .sticpl.cpl
Scheduled Tasks . . . . . . . . . . . . . . . . . . . . . . . . .control schedtasks
Security Center . . . . . . . . . . . . . . . . . . . . . . . . . .wscui.cpl
Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .services.msc
Shared Folders . . . . . . . . . . . . . . . . . . . . . . . . . .fsmgmt.msc
Shuts Down Windows . . . . . . . . . . . . . . . . . . . . .shutdown
Sounds and Audio . . . . . . . . . . . . . . . . . . . . . . . .mmsys.cpl
Spider Solitare Card Game . . . . . . . . . . . . . . . .spider
SQL Client Configuration . . . . . . . . . . . . . . . . . .cliconfg
System Configuration Editor . . . . . . . . . . . . . . .sysedit
System Configuration Utility . . . . . . . . . . . . . . .msconfig
System Information . . . . . . . . . . . . . . . . . . . . . .msinfo32
System Properties . . . . . . . . . . . . . . . . . . . . . . .sysdm.cpl
Task Manager . . . . . . . . . . . . . . . . . . . . . . . . . . .taskmgr
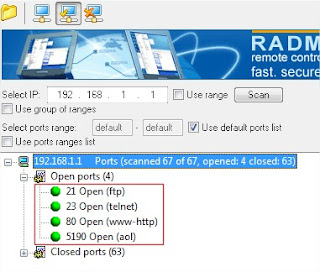
TCP Tester . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .tcptest
Tweak UI (if installed) . . . . . . . . . . . . . . . . . . . .tweakui
User Account Management . . . . . . . . . . . . . . . .nusrmgr.cpl
Utility Manager . . . . . . . . . . . . . . . . . . . . . . . . . .utilman
Windows Address Book . . . . . . . . . . . . . . . . . . .wab
Windows Address Book Import Utility . . . . . . .wabmig
Windows Backup Utility (if installed) . . . . . . . .ntbackup
Windows Explorer . . . . . . . . . . . . . . . . . . . . . . . .explorer
Windows Firewall . . . . . . . . . . . . . . . . . . . . . . . .firewall.cpl
Windows Magnifier . . . . . . . . . . . . . . . . . . . . . . .magnify
Windows Management Infrastructure . . . . . . .wmimgmt.msc
Windows Media Player . . . . . . . . . . . . . . . . . . . .wmplayer
Windows Messenger . . . . . . . . . . . . . . . . . . . . . .msmsgs
Windows Picture Import Wizard . . . . . . . . . . . .wiaacmgr (camera connected)
Windows System Security Tool . . . . . . . . . . . . .syskey
Windows Update Launches . . . . . . . . . . . . . . . .wupdmgr
Windows Version . . . . . . . . . . . . . . . . . . . . . . . .winver
Windows XP Tour Wizard . . . . . . . . . . . . . . . . . .tourstart
Wordpad . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .write
 12/30/2011 06:24:00 AM
12/30/2011 06:24:00 AM
 K.D
K.D






 When it comes to hacking, every other guy tends to tape the "hacker" word with his name/codename without even realizing its significance. Then there is Facebook ...Have a look at it -
When it comes to hacking, every other guy tends to tape the "hacker" word with his name/codename without even realizing its significance. Then there is Facebook ...Have a look at it -