1 Imagine ur cell battery is very low, u r expecting an important call and u don't have a charger.
Nokia instrument comes with a reserve battery. To activate, key is "*3370#"
Ur cell will restart with this reserve and ur instrument will show a 50% incerase in battery.
This reserve will get charged when u charge ur cell next time.
*3370# Activate Enhanced Full Rate Codec (EFR)-Your phone uses the best sound quality but talk time is reduced by approx. 5%#3370# Deactivate Enhanced Full Rate Codec( EFR)
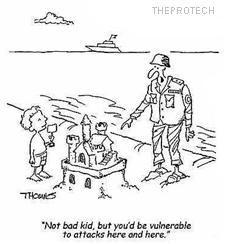
Top 10 Tricks to exploit SQL Server Systems
Whether it is through manual poking and prodding or the use of security testing tools, malicious attackers employ a variety of tricks to break into SQL Server systems, both inside and outside your firewall. It stands to reason then, if the hackers are doing it, you need to carry the same attacks to test the security strength of your systems. Here are 10 hacker tricks to gain access and violate systems running SQL Server.
1. Direct connections via the Internet
These connections can be used to attach to SQL Servers sitting naked without firewall protection for the entire world to see (and access). DShield's Port Report shows just how many systems are sitting out there waiting to be attacked. I don't understand the logic behind making a critical server like this directly accessible from the Internet, but I still find this flaw in my assessments, and we all remember the effect the SQL Slammer worm had on so many vulnerable SQL Server systems. Nevertheless, these direct attacks can lead to denial of service, buffer overflows and more.
1. Direct connections via the Internet
These connections can be used to attach to SQL Servers sitting naked without firewall protection for the entire world to see (and access). DShield's Port Report shows just how many systems are sitting out there waiting to be attacked. I don't understand the logic behind making a critical server like this directly accessible from the Internet, but I still find this flaw in my assessments, and we all remember the effect the SQL Slammer worm had on so many vulnerable SQL Server systems. Nevertheless, these direct attacks can lead to denial of service, buffer overflows and more.
13 Awesome, Must Try Notepad Tricks
In on of my previous post, i shared notepad trick allowing the user to test Anti-Virus just clicking a file created using notepad ! In this post, however i have decided to compile the entire list of notepad tricks instead of writing separate posts for each one of them. Here goes the top 10 notepad tricks .
1.This App Can Break
This is one of the most popular notepad tricks because of its mysterious nature. In order to get an idea as to what this trick does, just follow the steps given below:
· Open Notepad.
· Type “this app can break” (without quotes).
· Save that file with any name and close it.
· Open It Again to see the magic.
Reason For This Behavior: It is known as the 4335 Rule. It means that if we enter four words separated by spaces, wherein the first word has 4 letters, the next two have three letters each, and the last word has five letters. Then Notepad Automatically hides the text into unknown code.
Top 10 Windows Built-In Command Line Tools
For many Windows users, the thought of using the Command Prompt is either a scary experience or something that they will never need. But for some, the command prompt is a powerful tool that can be far more useful than many graphical tools available in Windows.
Being a System Administrator, I constantly use the command prompt, mostly because I access systems remotely and many tasks can be performed quickly with out the graphics over head (even though connecting via Terminal Server is very convenient).
JSKY - Free Vulnerability Scanner
With hordes of vulnerability scanners and frameworks launching everyday (mostly commercial) Jsky makes an impressive attempt to set itself apart by keeping it free and keeping it real by packaging everything in a small package. Don't be fooled by its small size, it packs quite a punch when compared to other professional packages considering its release version.Good vulnerability scanner ? check ! Web backdoor and SQL Injection? Check ! Directory traversal,sensitive directory and file scan? check ! Jsky is quite promising in its features..
Jsky packs powerful web spider and multi-threaded scanner which crawls hundreds of thousands of pages with ease & allows to extract links from JavaScript and flash.It uses Pangolin as its engine and allows for advanced and in-depth SQL injection,and hence can detect these vulnerabilities exactly with no sweat unlike others which using method of Pattern Matching.Supported databases include Oracle, MSSQL, Mysql, Informix, DB2, Access, Sqlite, Sybase, PostgreSQL and even more. Jsky has a modular design which allows for everybody to code and share their custom modules. Also a XML-based vulnerability file system and an integrated a Web vulnerability executive parser means you can design a vulnerability just by editing the XML file, no need to code any program.
The best part ? ITS FREE !
The best part ? ITS FREE !
Microsoft Visual Studio 2008 Professional Edition
Professional Edition was engineered to support development projects that target the Web (including ASP.NET AJAX), Windows Vista, Windows Server 2008, The 2007 Microsoft Office system, SQL Server 2008, and Windows Mobile devices. The number of platforms that developers must target to meet business needs is increasing rapidly. Visual Studio 2008 Professional Edition provides the integrated toolset for addressing all of these needs by providing a superset of the functionality available in Visual Studio 2008 Standard
Basics of Javascript Injection
JavaScript is a widely used technology within websites and web based applications. JavaScript can be used for all sorts of useful things and functions. But along with this comes some additional security issues that need to be thought of and tested for. JavaScript can be used not only for good purposes, but also for malicious purposes.JavaScript injection is a nifty little technique that allows you to alter a sites contents without actually leaving the site.This can be very usefull when say, you need to spoof the server by editing some form options.JavaScript injection is a fun technique that allows you to change a websites content without leaving the site, reloading the page, or saving the site to your desktop. It can be very useful when you need to change hidden data before you send it to the server. Let’s start with some basic injection techniques.
A website tells u if your computer ports are hacked or not
Check if Ur Ports are Hacked or NOT
info:Port Scan
This server will now attempt to open several common ports on your computer. The results of these attempts will be displayed on this page as Open, Closed, or Secure:
If your firewall is configured to block a port, and it is operating correctly, you will see Secure and an event will be logged on your firewall.
A Closed port indicates that the port is reachable but there is no program currently accepting connections there.
If the port is indicated as Open there is an application or service on your computer actively accepting connections.
The time to check each port will range from less than a second up to 20 seconds. Ports which are Secure will take the most time and if u are secured after the test ends tells u
Test complete.
No open ports were found
http://probe.hackerwatch.org/probe/probe.asp
Check it out
info:Port Scan
This server will now attempt to open several common ports on your computer. The results of these attempts will be displayed on this page as Open, Closed, or Secure:
If your firewall is configured to block a port, and it is operating correctly, you will see Secure and an event will be logged on your firewall.
A Closed port indicates that the port is reachable but there is no program currently accepting connections there.
If the port is indicated as Open there is an application or service on your computer actively accepting connections.
The time to check each port will range from less than a second up to 20 seconds. Ports which are Secure will take the most time and if u are secured after the test ends tells u
Test complete.
No open ports were found
http://probe.hackerwatch.org/probe/probe.asp
Check it out
 11/26/2010 08:35:00 AM
11/26/2010 08:35:00 AM
 K.D
K.D